In today’s rapidly evolving digital landscape, Virtual Private Networks (VPNs) have emerged as indispensable tools that offer many advantages for businesses seeking secure and efficient network solutions. As organizations expand their geographical reach, accommodate distributed teams, and embrace the benefits of remote work, the need for VPN technology has become a critical concern. VPN types cater to distinct use cases, ranging from the best VPN for remote access, which ensures secure connections for off-site employees, to VPNs in networking, facilitating seamless connectivity between geographically dispersed offices.
Furthermore, businesses increasingly prioritize the most secure VPN protocol to protect sensitive data from threats and eavesdropping. With many options available, the question “What type of VPN is best” becomes pivotal for organizations seeking to fortify their network infrastructure and ensure uninterrupted productivity in the face of contemporary challenges. Let us embark on this exploration together as we delve into the world of business VPNs, equipping you with the knowledge and insights necessary to navigate the dynamic realm of secure network communication.
In this comprehensive guide, we’ll explore the main types of business VPNs, delving into the best VPN for remote access, the pivotal role of VPNs in networking, the most secure VPN protocol, and the essential factors to consider when determining the ideal VPN type for your organization.
The Devices and Resources within a Corporate Network
A VPN ensures secure connections between employees’ devices and these network resources, ensuring that data transmission remains private and protected from external threats.
A corporate network encompasses various devices and resources that enable business operations, including:
- Network Devices (e.g., NAS, printers, NVR)
- Software as a Service (SaaS) applications
- Systems
- Cloud networks
The Importance of a VPN in Networking
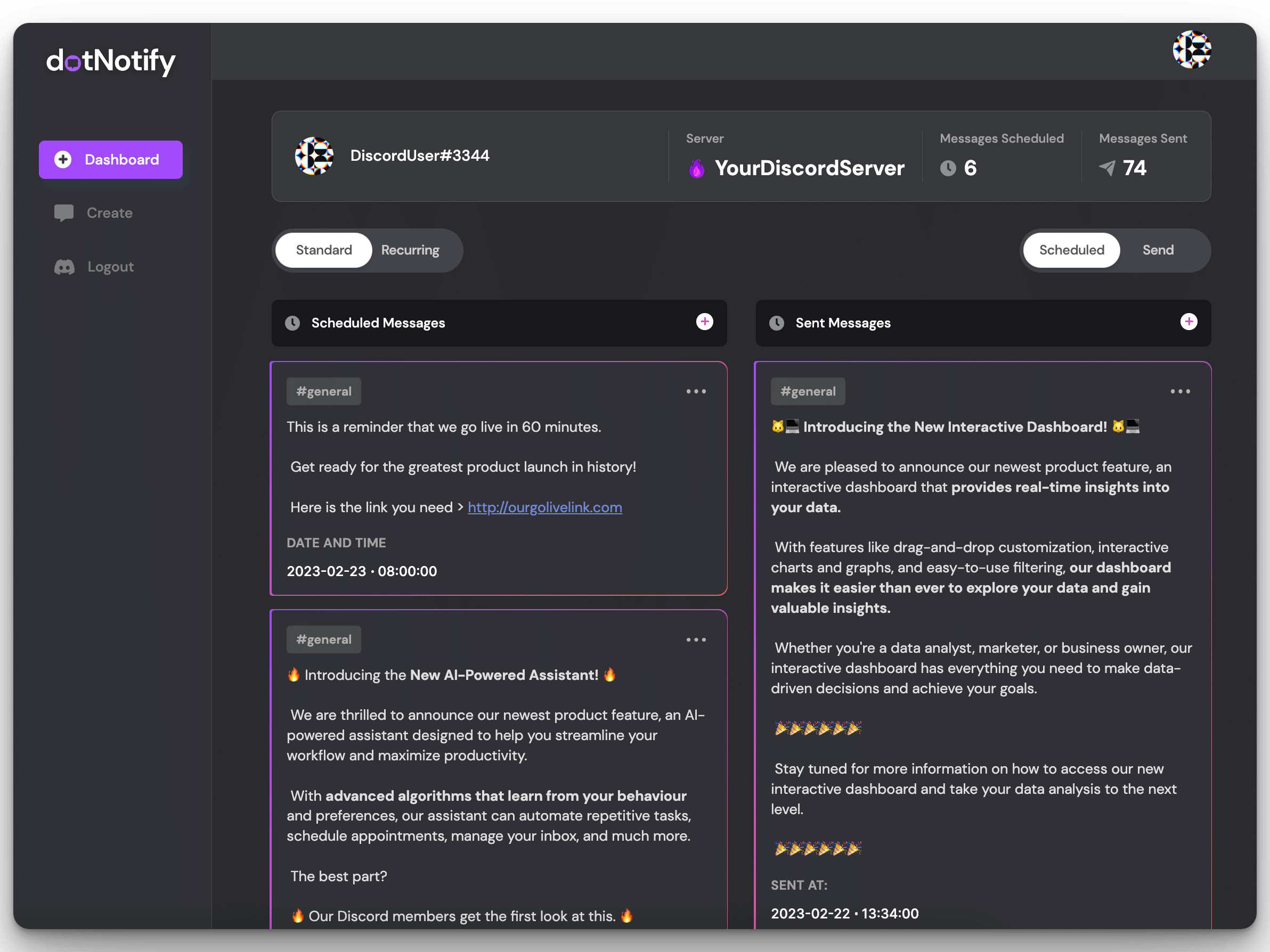
A VPN connection establishes a secure link between a VPN client (installed on the user’s device) and a VPN gateway. The gateway can be a network device like a router, firewall, or dedicated server interconnecting users and systems. At GoodAccess, they utilize distributed virtual private gateways worldwide, eliminating the need for customers to build complex infrastructures for VPN usage.
Employees working outside the office frequently use unsecured public networks, such as Wi-Fi, to access files, data, and systems over the Internet. However, these public networks can be vulnerable to hacking and cyberattacks. A VPN addresses this concern by creating a secure tunnel for data transmission, preventing unauthorized access to the business network.
The Benefits of a VPN for Your Business
- Secure Remote Access: VPNs enable employees to securely access the business network from any location, including remote work settings. This ensures seamless collaboration and access to critical systems and data.
- Protection from Hacking: By encrypting data transfer, a VPN makes it challenging for hackers to intercept and exploit sensitive information. This enhances the overall security of the communication over networks.
- Secure Communication on Public Networks: When employees use public Wi-Fi networks at places like hotels, airports, or cafes, a VPN encrypts all data transmitted, safeguarding it from potential cyberattacks.
- Anonymity: A VPN hides the user’s IP address, preventing the tracing of online behavior back to the business. This adds an extra layer of privacy and confidentiality to online activities.
- Compliance: With a VPN, businesses can monitor network activity, ensuring compliance with data protection regulations like GDPR.
Different Types of VPNs and Their Uses
VPNs are valuable tools for creating secure private connections between devices and servers. Depending on their intended usage, VPNs can be categorized into two main types:
- Business VPNs: These VPNs cater to the specific needs of businesses and organizations. They offer additional features and functionalities tailored for managing employees’ access to corporate networks and applications.
- Personal VPNs: Geared toward individual users, personal VPNs are commonly used to enhance online privacy and security. They safeguard identities, enable access to region-restricted content, and provide a secure public Wi-Fi connection.
Challenges of Using Personal VPNs for Businesses
While personal VPNs may be suitable for individual needs, they lack the robust management, configuration, and security features businesses require. Personal VPNs do not offer provisions for controlling access to corporate networks, detecting cyber threats, or ensuring applications remain invisible to unauthorized users. As a result, personal VPNs are ill-suited for companies, especially remote enterprises seeking comprehensive protection against cyberattacks.
Understanding VPN Topologies and Their Applications
The various types of VPNs can be distinguished based on their topologies, which refer to how their technology is structured:
- Remote Access VPN: These VPNs are primarily employed in companies where employees need to access data, LANs, and applications hosted within the organization’s premises. They enable secure connections for remote workers to access resources from external locations.
- Site-to-Site VPN: Ideal for companies with geographically distant offices or branches, site-to-site VPNs establish connections between these locations. They facilitate seamless communication and resource sharing between different sites.
- Cloud VPN: This type of VPN combines the benefits of both remote access and site-to-site VPNs. Delivered as a dedicated VPN service from the cloud eliminates the need for complex infrastructure setup and maintenance. Cloud VPNs provide a secure and scalable vpn solution for businesses.
Delivery Methods for VPN Implementation
The delivery of VPN services can be achieved through three main approaches:
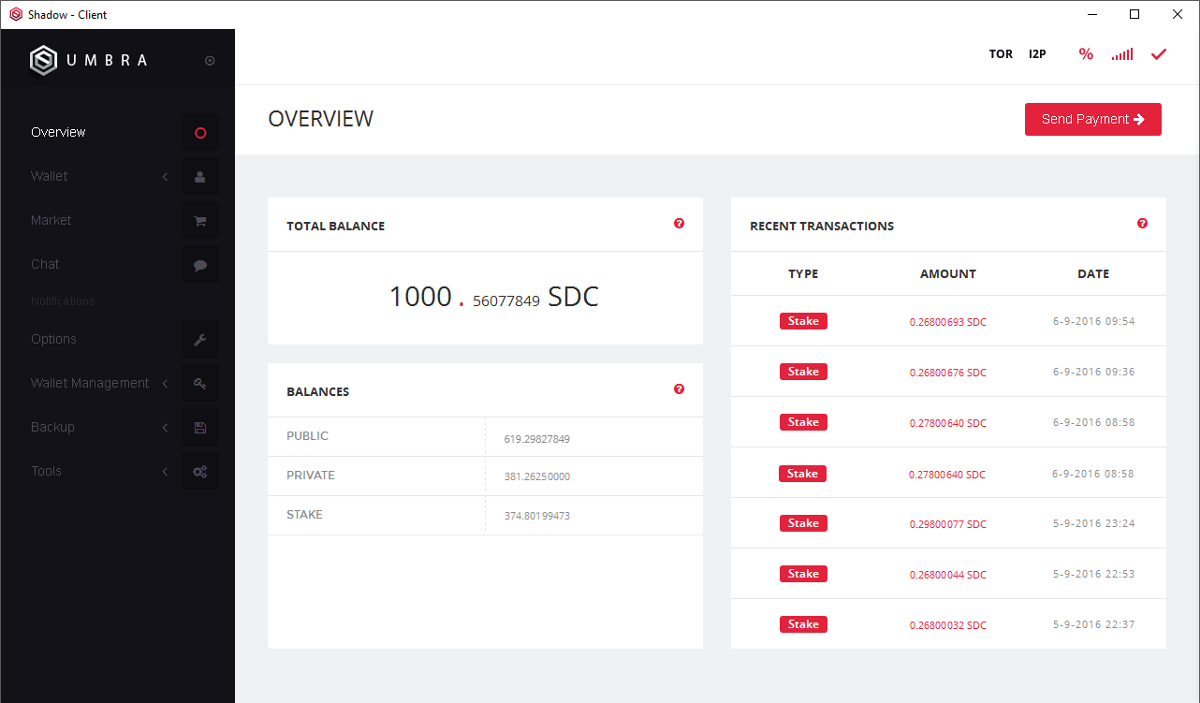
- Hardware VPN: This implementation requires dedicated hardware, such as routers or firewalls, configured specifically for VPN purposes. It involves significant investment in building and maintaining the necessary infrastructure.
- Software VPN: A software VPN is run from a private data center, providing ease of management and user-friendliness. However, it still necessitates the setup of a VPN infrastructure.
- Cloud VPN: Delivered as a service from the cloud, a cloud VPN eliminates the need for hardware. It offers stability, easy setup, and configuration, making it a cost-effective and efficient business solution.
Choosing the Right VPN for Your Business
In conclusion, VPNs have become indispensable tools for businesses in the digital era, facilitating secure remote access and protecting sensitive data. Understanding the types of VPNs, such as remote access and site-to-site, helps businesses make informed choices to suit their specific needs.
To achieve the best results, businesses can opt for a cloud business VPN that combines the advantages of remote access and site-to-site capabilities. The benefits of such a VPN include reliability, scalability, high speed, and cost-effectiveness, making it the ideal solution for modern businesses.
Embracing a secure VPN like GoodAccess ensures streamlined network connections and protects businesses against cyberattacks. By prioritizing the implementation of the right VPN solution, businesses can thrive in the increasingly connected and remote-oriented business landscape.

I’m Kelly Hood! I blog about tech, how to use it, and what you should know. I love spending time with my family and sharing stories of the day with them.